The ups and downs of running enclaves in production
Cian Butler SRE@Evervault
Some Context
Evervault offers tooling for data security and compliance.
- Encryption Proxy
- Secure Serverless Functions
- Embeddable UI components
- Enclaves
Relay
The Problems
- Piles of custom automation.
- Nascent Libraries
- Observability
- Userspace Networking
- Time slippage
Nascent Libraries
pub struct NsmConnection(i32);
impl NsmConnection {
pub fn try_new() -> Result<Self, NsmConnectionError> {
let nsm_fd = nitro::driver::nsm_init();
if nsm_fd < 0 {
return Err(NsmConnectionError::InitFailed);
}
Ok(Self(nsm_fd))
}
}
impl std::ops::Drop for NsmConnection {
fn drop(&mut self) {
nitro::driver::nsm_exit(self.fd());
}
}
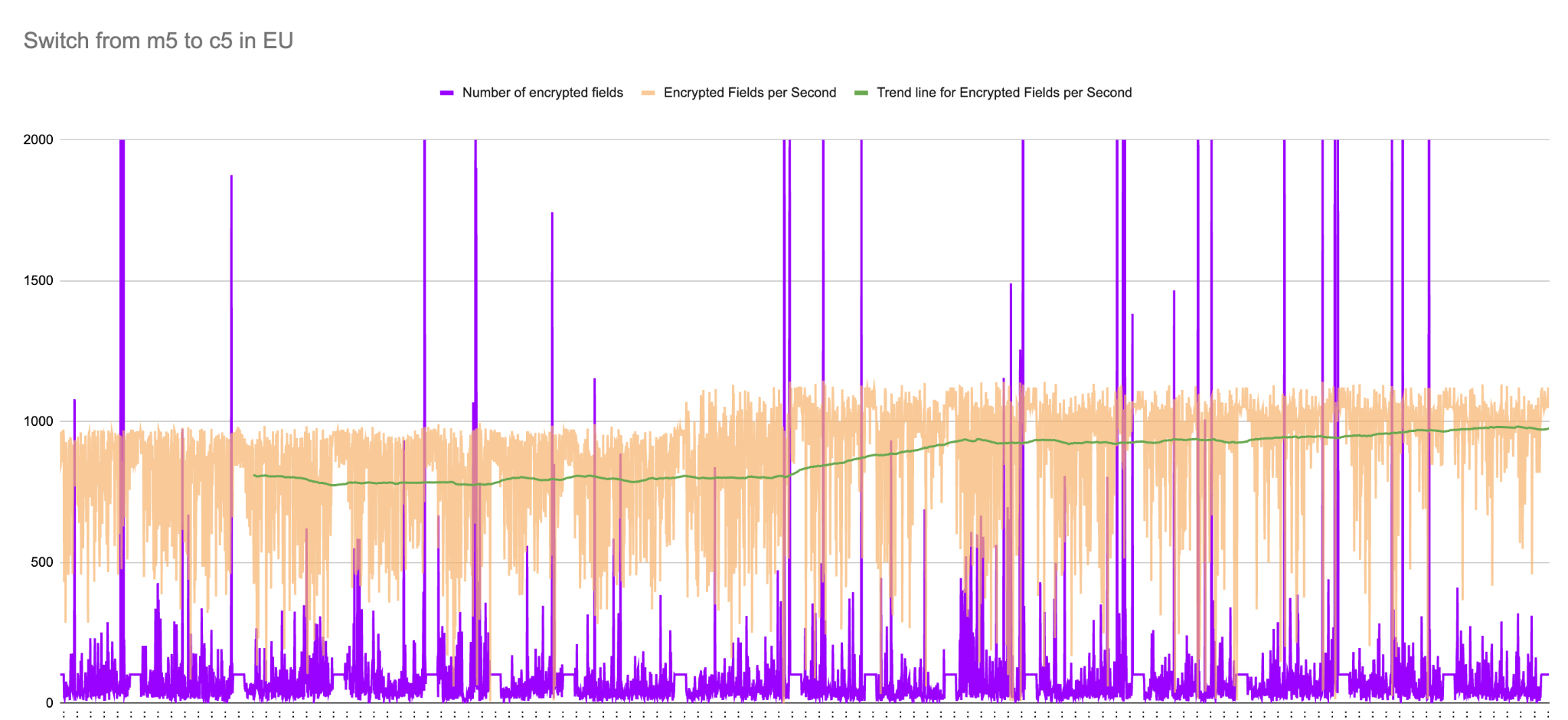
Observability

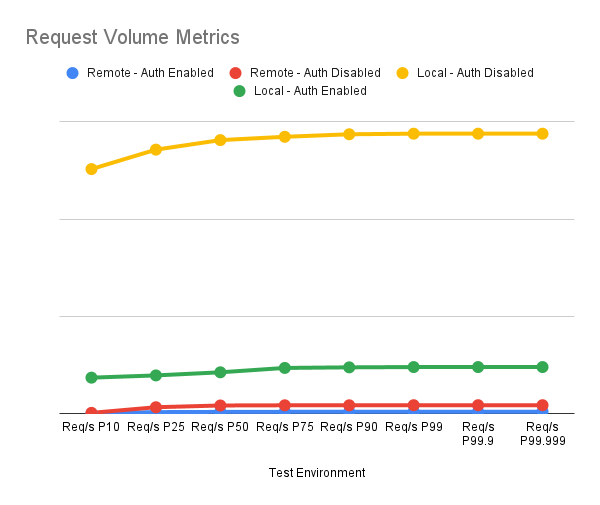
Userspace Networking
Time slippage
There is no NTP in enclaves.
Evervault Enclaves